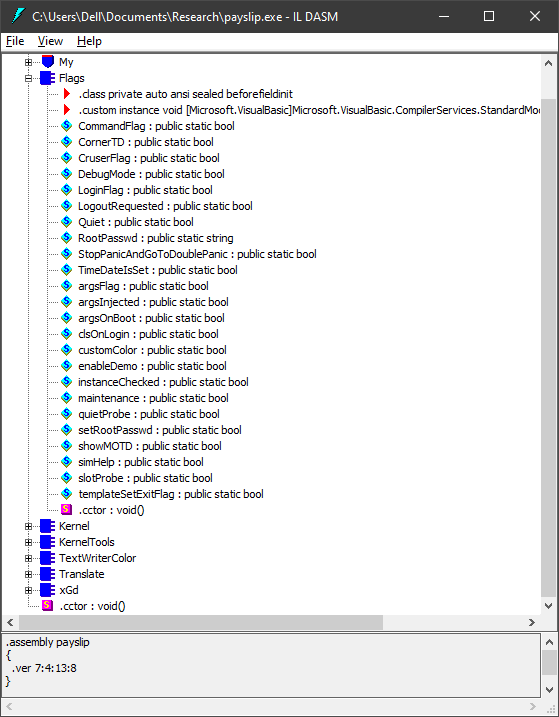
The May 2019 Payslip virus, and its usage of some of KS's features
public static string KernelVersion = Assembly.GetExecutingAssembly().GetName().Version.ToString();
public static string[] BootArgs;
public static string[] AvailableArgs;
public static string[] availableCMDLineArgs;
public static string MOTDMessage;
public static string HName;
public static string MAL;
public static string EnvironmentOSType;
static Kernel() // Generated by JetBrains dotPeek
{
string[] strArray1 = new string[Convert.ToInt32(3.41886116991581 + Math.Sqrt(2.5))];
strArray1[0] = "quiet";
strArray1[1] = "cmdinject";
label_1:
int num1 = 322610553;
string[] strArray2;
while (true)
{
uint num2;
switch ((num2 = (uint) (num1 ^ 1915212704)) % 9U)
{
case 0:
num1 = (int) num2 * -685199074 ^ 818517677;
continue;
case 1:
strArray1[Convert.ToInt32(5.41421356237309 - Math.Sqrt(2.0))] = "help";
Kernel.AvailableArgs = strArray1;
num1 = (int) num2 * -85093751 ^ -1759328859;
continue;
case 2:
goto label_3;
case 3:
strArray2[0] = "createConf";
strArray2[1] = "promptArgs";
num1 = (int) num2 * 1980815017 ^ -1632831499;
continue;
case 4:
Kernel.EnvironmentOSType = Environment.OSVersion.ToString();
num1 = (int) num2 * -1749997108 ^ -1153977823;
continue;
case 5:
strArray2 = new string[Convert.ToInt32(2.0 * 1.5)];
num1 = (int) num2 * 330882450 ^ 1511576150;
continue;
case 6:
goto label_1;
case 7:
strArray2[Convert.ToInt32(3.0 - Math.Ceiling(1.0))] = "testMod";
Kernel.availableCMDLineArgs = strArray2;
num1 = (int) num2 * 1472650476 ^ 1747686761;
continue;
case 8:
strArray1[Convert.ToInt32(3.0 - Math.Sqrt(1.0))] = "debug";
strArray1[Convert.ToInt32(5.0 - Math.Round(1.5))] = "maintenance";
num1 = (int) num2 * -1989761204 ^ -1809828870;
continue;
default:
goto label_11;
}
}
label_3:
return;
label_11:;
}Last updated